94 is the average number of attacks on a website a day!
As the virtual world evolves so do the hackers. This means that our online security practices should at least keep up, our, better yet, outpace the attackers.
As you’ll see below, research shows that way too many websites take little to no protection measures and thus become the easy catch. Let’s make sure this isn’t your website!
In this article we are tackling the following issues:
- What CMS solutions are the most vulnerable and why?
- What CMS solutions are the most secure and why?
And sharing security tips for CMS platforms (canned and custom):
- How to make your off-the-shelf CMS more secure?
- How to make your custom CMS more secure?
What CMS Solutions are the Most Vulnerable and Why?
The most vulnerable websites are the ones that run on the popular off-the-shelf CMS platforms. And especially the ones that take little to no protection measures.
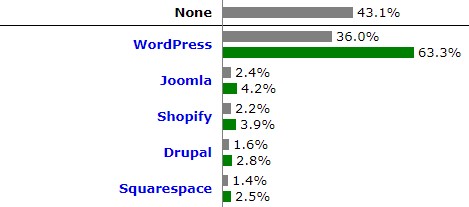
Currently, the most popular CMS platforms are WordPress, Joomla, Shopify, and Drupal. While WordPress is the clear winner, covering 63.3% of all sites on the web.
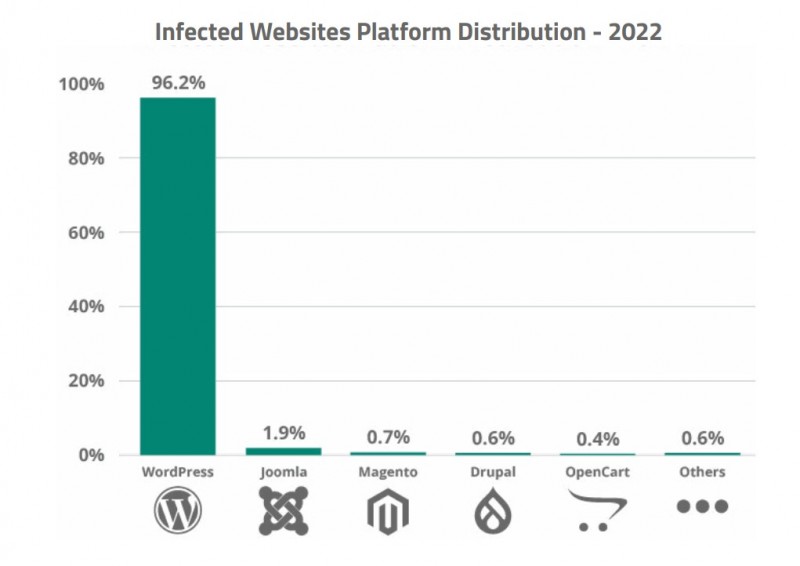
And this is the platform that gets hacked the most. According to Sucuri (CMS security software provider), 96.2% of all infected websites in 2022 were on WordPress.
Oddly enough, most of the vulnerabilities of these systems come from their popularity. Here are the main reasons why hackers prefer to attack websites that run on popular CMS platforms:
- Everybody knows about these platforms, including hackers
- Everybody has access to the source code, especially with open source solutions
- They can be ‘hacked in bulk’, as once someone finds a hole in a platform he/she can attack ALL of the websites that use it in one go
- There are many unqualified developers that fail to take proper security measures.
Yet, there are ways to make even a WordPress website more or less a secure place for both your visitors and you. We’ll talk about them below.
What CMS Solution is the Most Secure and Why?
First, let’s admit that a properly built custom CMS is the most secure solution there is.
By ‘custom’ we mean a CMS solution that web developers build from scratch, usually with a programming framework of their choice. And by ‘properly built’ we mean adhering to the best security and coding practices (more on that later).
So here is what makes a custom CMS more secure than an off-the-shelf one:
- Custom CMS platforms are ‘one of a kind’, so no one but you and your team will know about it and how it works
- Only you and your development team will have access to the code
- Hackers will have to do all the hard work to attack only one website, as opposed to millions that run on some popular platform like WordPress.
Of course, having a custom CMS doesn’t guarantee that you won’t be attacked. But, as you see, your website won’t look so attractive to hackers anymore.
How to Make Your Off-the-Shelf CMS More Secure?
Here we’ll cover some security basics for canned solutions, as well as talk about some not so straightforward solutions that work for us.
So here are the things you can do to keep your website safe:
- Update your CMS platform
- Hide your platform and admin panel
- Use firewall
- Scan your off-the-shelf CMS and any third-party solutions you use with it for viruses
- Make your website static.
Let’s take a closer look at each of them.
Updates
In 2022, over 50% of all CMS applications were out of date at the point of infection. So over half of WordPress users with the majority of Joomla and Drupal users don’t update their websites!
Why is it important? And why is this so dangerous not to update your platform?
Because these popular platforms are under the constant radar of hackers. They relentlessly study WordPress, Joomla, Drupal, and others to find their vulnerabilities.
If we are lucky, the good guys (the core team or contributors) will find holes in your CMS platform and create patches for them before the bad guys do. This is what happens when the CMS platform issues updates. The sooner you deploy them, the better the chance that hackers won’t take advantage of these platform bugs.
As soon as your platform issues an update, the information about the detected bugs was already made public. So those who don’t update in the nearest hours become the easy targets.
“You should proceed under the assumption that every Drupal 7 website was compromised unless updated or patched before Oct 15th, 11 pm UTC; that is 7 hours after the announcement.” Sucuri.
This is an example of how fast everything happens. So don’t put off your updates unless your website is static (more about that below)!
And make sure you update not only the platform but also other software you use like third-party plugins and your theme. Actually, in our experience, most of the vulnerabilities come from third-party plugins and themes, not the platform.
Hide Your Platform and Admin Panel
If you don’t change the generic URL of your admin panel (www.domain.com/wp-admin for WordPress), hackers will have no trouble finding it and determining your platform.
Knowing your platform will give a lot of advantages to hackers. They will have the access to the source code and likely studied the common vulnerabilities of your CMS.
Besides, they will know the URL of your admin panel and will try to use the brute-force tools to break in. This is especially dangerous if you have weak passwords and unprotected access.
So here is what you can do to hide your platform and admin panel:
- Change URLs to admin panel
- Make sure hackers won’t determine your platform by looking at your HTML code
- Create a whitelist of IP addresses that will be allowed to restricted areas
- Use strong passwords
- Use intrusion prevention software like Fail2Ban.
Hackers can trace your platform with a help of the generic URLs and, sometimes, by looking at your HTML code.
Your developers can hide your platform by rewriting the generic URLs manually or with a help of a plugin. And they can make sure HTML code doesn’t show any signs of your CMS platform.
You can also create a list of IPs of all the people that are allowed to the restricted areas of your website and ban all others.
Then you can use some password generator to generate safe passwords for all users. And don’t forget to keep and exchange them safely.
Finally, your developers can install some intrusion prevention software (e.g. Fail2Ban) to save you from brute-force attacks. That is when hackers will be trying endless combinations of logins and passwords to access your admin panel. Fail2Ban, or a similar tool, will set rules for your firewall (more on that below) to limit the number of attempts a user has to log in.
Use Firewall
Use the firewall to monitor and control incoming traffic. The firewall will shield your website from unwanted traffic and make sure all back-end ports are blocked.
You can also use it together with your intrusion prevention software (e.g. Fail2Ban). In such a way firewall will ban IPs of those users who fail to enter the right login and password in a limited amount of attempts within a set timeframe (e.g. more than 3 wrong passwords in one minute).
The firewall will also prevent attacks on your network infrastructure. It will block the server and individual components, e.g. your database.
Scan for Viruses
It is also a good idea to scan your CMS for viruses and vulnerabilities. Firstly, you might be already infected and don’t even know about it. Secondly, you should know about the weak spots of your website to protect yourself before hackers find them.
Here are the types of scanning you can do:
- Scan for malware
- Scan for vulnerabilities.
There are many tools for that. Some are platform-specific, like all-in-one security plugins for WordPress or WPScan, while others are uni-platform, like Sucuri.
Make it Static
This solution will transform your website into a static one, consisting only of HTML files with CSS and JavaScript.
During the attacks, hackers often change existing scripts or inject new ones to perform undesired actions. So if your website is static, i.e. doesn’t have any scripts, hackers won’t be able to find them and exploit their vulnerabilities.
The outside world, including hackers, won’t see any back-end and won’t be able to detect what CMS platform you’re using. While in reality your back-end will be hidden on a subdomain with a double authorization required to view it and to access the admin panel.
Having a static website means that each time you will post or edit the content you’d have to generate the updated static version of your website. You can do this with a help of such solutions as Simply Static Plugin for WordPress or Hugo for any platform.

Making your website static will give you the following benefits:
- Protect you against the common hacker attacks (like injecting malicious code into your site)
- You won’t need to update your CMS as often (this can be a huge relief when you have backward compatibility issues)
- Your website will become a lot faster (no need to render your website every time someone visits).
Despite its benefits, this solution is definitely not for everyone. It works great for smaller websites with occasional content updates (a couple of times a day or even a week). But if your website depends on a lot of dynamic features like database-driven forms or searching and matching (e.g. news websites, dating apps), then this solution is not for you.
How to Make Your Custom CMS More Secure?
The truth is that even a poorly secured custom CMS will be more secure than WordPress. As I’ve already mentioned, with custom programming, your code will be unique and no one but you and your team will have the access to it.
However, you must be reading this article because you don’t want to take chances.
So here are the best ways to make your CMS secure:
- Use a framework and follow its best security practices
- Use only trusted third-party libraries.
There are general best coding practices that developers have to follow to create reliable and secure software. And there are also framework-specific best practices. These will guide even inexperienced programmers in developing a safe website.
In our experience, following the best practices and using only trusted third-party resources, when we must, is usually enough to make a secure system.
As the need arises, we take some extra measures to prevent the attacks, e.g. encryption and tokenization among others.
All in all, hiring a skilled web development team is the best thing you can do to protect the CMS of your website. They will follow all the best practices and go for extra measures to make your website secure.
Conclusion
Let’s sum up.
If you going for the most secure CMS solution, custom-built CMS will be a safe choice. It may not be the easiest or the cheapest one to start with, but with a skilled team, you will get a nearly bulletproof solution.
In case custom programming is not an option for you, make sure you take all the necessary measures to protect your off-the-shelf CMS. Hide your platform and admin panel, update often, scan for viruses, use firewall and/or make your website static.
The bottom line is that it is all about getting the right people to work on your website!
Get a FREE consultation on how to make your website bulletproof!
Contact UsRate this article!
5







 Sign in with Google
Sign in with Google
Comments (0)