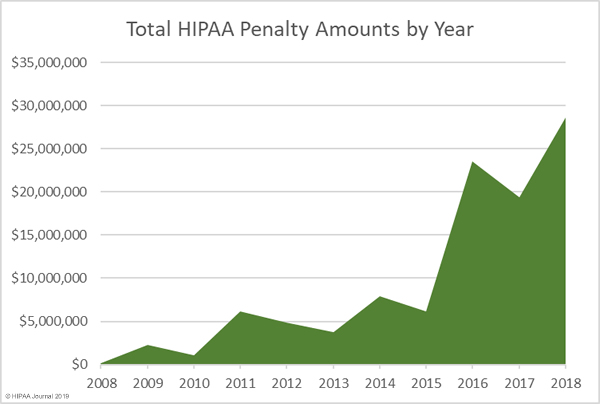
$134,828,772 is the total amount of penalties to date that has been paid by organizations and individuals for noncompliance with HIPAA.
How does this make you feel?
Stressed, neutral, or motivated?
As a mental health professional, you haven’t been trained to deal with technology and cybersecurity, so it is only natural to be fearful and overwhelmed by rapidly changing privacy regulations.
We’re sure you are well aware of your duty to protect your patients’ information and you probably know how to do this physically (locking desks and using noise machines). But what about the digital information? How do you protect your emails, video calls, electronic records, messages, etc?
If you don’t have the answer yet and are looking for guidance, we’re here to help.
1. Understanding HIPAA Regulations for Mental Health Practice
What is HIPAA?
The Health Insurance Portability and Accountability Act (HIPAA) is a set of rules that individuals and organizations have to follow to protect patient information.
In a nutshell, HIPAA is about safeguarding the confidentiality, availability, and integrity of the PHI.
This act is very extensive and covers a wide array of topics like:
- What information should be protected
- Patients’ rights in regards to his/her health information
- To whom and in what circumstances the information can be disclosed
- In what way it should be protected
In this article, jointly with Legal Nodes, our legal partner, we will do our best to cover the key aspects of HIPAA and Mental Health Practices.
Do I Have to Comply With HIPAA Laws in Mental Health?
Yes, if you directly bill insurance.
HIPAA states that all healthcare providers that engage in covered transactions have to comply. These are the type of transactions like claims, eligibility, payments, benefits coordination, and others. To be 100% sure, check if you are a covered entity with the official tool.
What happens if you’re not a covered entity?
Don’t do a happy dance just yet. You still have to abide by your ethics code, which also obliges you to protect your patients’ information. It’s just that HIPAA provides more or less comprehensive standards for the security of electronic patient information, so you might as well use them.
What happens if I don’t comply?
[Warning! This passage may raise your stress levels.]
A number of bad things.
You can be fined for noncompliance and you can be sued by your patient. Worst of all, this can happen at the same time.
And HHS considers any impermissible use or disclosure of PHI a breach. Which means that even if someone has looked over your shoulder and saw things he was not authorized to see, it is considered a breach. You could get away with this only if you could prove that there is a very low probability that the information hasn’t been compromised, which is not easy to do.
Moreover, you can be fined solely for noncompliance, even if there is no breach yet! HHS Office for Civil Rights doesn’t actually penalize for breaches themselves, but rather for noncompliance.
How can anyone know? First of all, from your colleagues, employees, patients, and a guy on the street who can report violations anonymously. Secondly, the number of random audits by OCR increases each year, so anyone can get ‘lucky’. Thirdly, you yourself are obliged to notify the patients whose data were compromised and the Secretary, should any breach occur.
So how bad are the fines?
Depending on the amount and severity of the violations penalties can be as low as $100 and as high as $1,500,000.
Sadly, many organizations have to add very expensive lawsuits with patients to that number.
To date, OCR has resolved 26,851 cases, resulting in millions of dollars in penalties.
Here is one example from the mental health field…
A network of mental health facilities in Alaska had a security breach resulting in compromising the records of 2,700 patients. Their information system has been infected with malware because they’ve failed to update their software. This costed $150,000 in fines to the organization.
2. MENTAL HEALTH INFORMATION COVERED BY HIPAA
Information Types
HIPAA protects information of individuals, which includes:
- Records, current state, and projection of the person’s mental health or condition. Mental health is about the psychological well-being of a person and one’s performance of the mental function. In a broad scope, it includes a person’s behavior, social activities, and fulfilling relationships with other people.
- Information on a person's mental disorders is also covered by the HIPAA in mental health scope, including information on alterations in thinking, mood, or behavior associated with distress or impaired functioning. Information on the healthcare services provided to the person. The history of relationships between the patient and a health care provider constitutes a discriminatory factor and thus also falls under the scope of HIPAA.
- Payment for mental health services. Most of the time, this information is tied to the provision of services. However, the mere history of payments for the services, including invoices, also receives the HIPAA protection.
HIPAA covers only identifiable information. This means that it must be linked or be possible to get linked to the personal identifiers, such as name, address, birth date, biometric data, Social Security Number, or other identifying information (HIPAA provides a list of 18 identifiers, which are non-exhaustive).
HIPAA pays specific attention to psychotherapy notes. The control over the psychotherapy notes is balanced between two parties:
- the mental health professional due to the personal character of the notes, and
- the patient, whose personal information is in notes.
Places of Storage
Certain HIPAA rules, such as security rules, set requirements for protected health information only in electronic form.
At the same time, the use and disclosure rules (Privacy Rule) also cover written and oral communications of the patient’s information.
Besides the common forms, such as medical files, patient documents, or history of treatment, protected information will also include:
- precontractual request for mental health services with an explanation of the patient’s concerns or problems;
- prescription of medication for a patient and medication/vaccination records;
- records of online therapy with patients, including video and audio;
- e-mails and other electronic communications with the patient regarding one’s mental health or treatment;
- a timetable of appointments with patients and time of start and end of sessions;
- assessments of the patient in the spreadsheet or other electronic document form;
- reports with the patient’s results from the laboratory or EKG results;
- diary of the patient’s mood, thought records, and self-assessment of one’s mental health (This can take an unusual form, such as data from the patient’s health app, which he/she shares with the doctor. For example, ThinkPacifica, an app for tracking mental health and automating a counseling, allows patients to share their activity and mood records with their counselors);
- cloud-based storage of the patient electronic records and their back-up copies.
Generally, mental health provider must ensure end-to-end protection: whether you receive patient information directly or indirectly, protect the information in all places of storage or processing.

Are you sure your EMR is safe?
Contact Us3. HIPAA Compliance for Mental Health Practice - The Roadmap
Feeling overwhelmed already? Have a small break, because this part is going to get even more intense.
If you are ready, let’s get to the nitty-gritty.
We’ve identified the following key aspects of HIPAA compliance for mental health practices:
- Collection and Use Rules
- Disclosure Rules
- Administrative Safeguards
- Physical Safeguards
- Technical Safeguards
- Breach Notification Rules

But before you dig in, we have to make a couple of warnings. First, HIPAA is very extensive and detailed. Thus, the purpose of this section is not to give exhaustive legal advice, but rather a road map and high-level overview of all the things you need to consider.
Second, HIPAA consists of two major parts - Privacy Rule and Security Rule. Privacy Rule is a general set of requirements for all forms of protected patient information (PHI) and Security Rule is for digital-only (ePHI). For the purposes of this article, we’ve combined all the requirements and standards into one list, because there are a lot of intersections between the two rules.
1. Collection and Use

As a part of fair practice, you must meet certain requirements before, during, and after the collection of patient information.
This section addresses the main rules on information collection and its use in mental health practice:
- Minimum Necessary rule;
- Authorization for other purposes;
- Privacy Notice; and
- Patient rights.
Minimum Necessary Rule
Minimization is a cornerstone principle of HIPAA protection. You can use and disclose only the minimum information required by the health service’s purpose. Minimum necessary covers three elements:
- a minimum amount of the collected information;
- a minimum amount of disclosed information, limited by the purpose of the disclosure; and
- a minimum number of recipients of the information.
Authorization for Other Purposes
If you decide to use the protected health information for other activities than counseling or related purposes, you’ll need official authorization from the patient.
The authorization must be specific, unambiguous, freely given, and written in plain language.
As an example, the use of patient information for marketing (except for face-to-face communications) requires specific authorization from the patient.
However, you don’t need consent from the patient to use his/her data for research purposes (subject to one of three additional safeguards).
Privacy Notice
Privacy Policy, also known as the Privacy Notice, is the company's statement that explains to individuals how the company collects, uses, and protects their personal information.
You should include the ‘what-when-how’ details on the use of the information, your contact details, inform about patient’s rights, explain your legal duties, includ an effective date, and a specific header.
You should also remember that you address the Privacy Notice to the patients, not to lawyers. The document must be unambiguous, understandable to concerned patients, and written in clear and plain language.
Thus, a 10-page document of legalese is likely to be an invalid Privacy Notice.
Unsure how to draft a consistent Privacy Notice?
Contact Legal NodesPatient Rights
It’s important that you respect the rights of your patients over their information. Your practice must let the patient exercise the following:
- access to the information - with a few exceptions (e.g. psychotherapy notes), the patient has the right to review and request a copy of the information you collected;
- correct (amend) the information if the information is inaccurate or out-of-date;
- be informed of disclosures to know all the recipients of the patient information upon the patient’s request;
- restrict disclosures (agreeing to comply with this right is not binding for the providers);
- choose the contact means, whether mail, email, or phone number; and
- complain to you, or worse to the state regulatory body.
Although according to official statistics, patient rights are not the most popular subject of HIPAA violations, the offense can be costly. In 2011, the regulatory body imposed one of the most severe penalties ($4.3 million) on a healthcare center for denying access to 41 patients.
2. Disclosure Rules

During the practice, you will have many situations where you might want or have to disclose patient records. In this section, we give tips on sharing the information on the eight most debated topics:
- Disclosure to the family;
- Rules on psychotherapy notes;
- Group therapy disclosures;
- Treatment, Payment, Health Care Operations;
- Service providers (Business Associates);
- Informal permission;
- Disclosures requiring authorization; and
- Necessary disclosures.
Disclosure to the Family
As a general rule, the patient must give permission to you to share his/her information with the family members.
However, if the family member acts as the patient’s representative (including the cases with minors), such a person has the full right to access the information.
At the same time, you can refuse access if you believe that the representative’s access can harm or threaten the patient. And if the patient is temporarily incapable of making decisions, you can decide whether to share the information with the family in the patient’s best interest or to prevent (or lessen) the harm to the patient.
Rules on Psychotherapy Notes
Disclosure of psychotherapy notes to any person, whether to family members or a business partner, requires ‘double authorization’:
- The patient cannot request the disclosure of the notes without your consent, because the notes contain your personal assessments that must remain confidential; and
- To disclose the notes to third parties, you’ll be required to obtain the patient's permission, because they contain her/his protected health information.
Group Therapy Disclosures
In group therapies, you will likely discuss the protected health information of patients with the other participants. It’s completely okay to share the patient’s information during group therapy under HIPAA. Before participating in the therapy, the patients understand and agree that other members of the group will hear their details. This agreement generally implies the patient’s consent to the disclosure of information.
Treatment, Payment, Health Care Operations
You don’t have to receive permission to share the information with your partners in:
- treatment (consultation regarding the patient, reference to another professional),
- payment (e.g., billing services), or
- health care operations (absolutely necessary for running the practice).
Service Providers (Business Associates)
Business associates are the services providers, such as CRM, online-therapy tools, or e-mail providers that receive access to the patient information.
You must conclude the Business Associate Agreement to ensure that the contractor will protect the information from unauthorized access and use it only to provide the services.
The absence of the agreement with the services provider may result in a breach of access to the patient records. At the end of 2018, Advanced Care Hospitalists PL was fined $500,000 for not having a policy on service providers and failing to have a Business Associate Agreement with its payment services provider.
Informal Permission
For disclosing contact details for treatment-related cases, the patient’s informal ‘yes’ will be sufficient. A good example is sharing the contact of the patient’s representative with the pharmacist to receive the patient’s prescriptions.
Disclosures that Require Authorization
A simple ‘yes’ won’t be sufficient in certain cases. You must obtain a proper authorization (as discussed before) where the disclosure is not related to the treatment nor prescribed by laws. For example, sharing the treatment details with other health providers for their own ends requires consent from the concerned patients.
Necessary Disclosures
Some disclosures are prescribed by law - so you’ll have to share the information even if you or the patient doesn’t want to. The necessary disclosure provides, among other things, for the following mental-health-related cases:
- legal requirements - if explicitly required by the other act, regulation, or court order;
- law enforcement - disclosure connected to the official inquiries;
- public health activities, such as the report of child or elder abuse, to prevent domestic violence, or in general injury or damage;
- and workers compensation requirements.
3. Administrative safeguards

This part is all about administrative policies and procedures, as well as knowing your privacy and security risks and managing them well.
Here we’ve compiled the following 9 standards as part of your administrative tasks to comply with the law:
- Risk Analysis and Management;
- Hire Security and Privacy Officers;
- Authorization and Access Management;
- Security Practice for Employees;
- National Provider Identifier (NPI) and Employer Identification Number (EIN);
- Security Incident Procedures;
- Contingency Plan;
- Evaluation.
Let’s go over each of them one by one.
Risk Analysis and Management
This is one of the most important parts of compliance because in this standard you have to identify your risks and think of ways to mitigate them. The following steps are mandatory:
- Conduct Risk Analysis to identify potential risks and assess their severity;
- Prepare risk management plans to specify what measures you’ll take to mitigate the risks you’ve found;
- Implement a sanction policy so that your employees were clear of what the consequences of noncompliance are;
- Regularly review the activity of your information systems to determine that no patient information has been leaked, breached, or accidentally destroyed.
Have a Security Official and Privacy Officer on the Team
According to HIPAA, you need to have a designated person or persons that will be responsible for putting the law to practice. There are two roles for this: Security Official and Privacy Officer.
The Privacy Officer takes care of the internal policies on the use and disclosure of the protected health information. The Security Official, on the other hand, should tackle the security practices in regard to electronic patient information (ePHI).
A person may combine the responsibilities for both positions, but make sure he/she is able to diligently perform both roles and doesn’t have a conflict of interest.
Authorization and Access Management
This standard requires you to make sure that only authorized people have access to your patients’ information.
For that you have to:
- Determine who in your practice gets access to what information (or no access at all);
- Have procedures that prevent unauthorized people to get access to ePHI; Ensure that access to ePHI is terminated for employees (contractors, partners, individuals that leave your practice);
- Document policies that establish and modify access to ePHI.
Security Practices for Employees
HHS states that unless you inform and involve your employees of what they should and shouldn’t do in regards to ePHI, it cannot be considered secure. Specifically, they’d like to:
- Regularly remind your employees of security practices and procedures they have to follow;
- Install, update and use anti-virus software;
- Have automatic log-in monitoring to make sure only authorized users to get access;
- Have procedures/tools to safely manage passwords.
National Provider Identifier (NPI) and Employer Identification Number (EIN)
To remain accountable before the patients and the government, you will be required to apply for the NPI - a 10-position, intelligence-free numeric identifier (10-digit number).
You must use this standardized identifier in all administrative and financial transactions, including insurance-related payments, billing of patients, and all daily operations.
For employment purposes, the Internal Revenue Service will issue an Employer Identification Number (EIN). This number will identify you in employment-related issues. You are supposed to include it in payroll and other direct or indirect employer-employee transactions.
Internal Policies and Security Incident Procedures
You must incorporate the rules on the use, sharing, and security of information into your corporate policies (do not confuse with Privacy Policy).
The documents should provide a step-by-step plan of action on:
- processing and disclosure of the information;
- compliance with patient requests and legal requirements (including breach notification);
- the use of the information for your own purposes; access management issues;
- instructions for how to deal with security incident; and
- documenting procedures.
Finally, the paperwork doesn’t end with policies and procedures. HIPAA requires you to document all efforts, notices, and other actions related to compliance with the act. To remain accountable, you will have to retain the documentation until six years after the date of its creation.
Do you need to develop the necessary policies quickly and cost-efficiently?
Contact Legal NodesContingency Plan
According to this standard, you also must have a contingency plan of what to do in case of emergency with ePHI like a power outage, vandalism, fire, etc. Your plan should include:
- Data backup;
- How lost data will be restored;
- Reminders to regularly review and test your contingency plan;
- A prioritized list of all apps used in your practice to know which ones to restore first.
Evaluation
Finally, you have to periodically evaluate how well these HIPAA standards are implemented and, when necessary, tweak something because of internal or external changes.
- Decide how often it makes sense to do the evaluation for your practice;
- Document the results of the evaluations;
- Make sure to implement any necessary changes according to the evaluation results.
4. Physical safeguards

Physical safeguards are about everything that you should and shouldn’t do to protect physical access to ePHI. Physical access implies access to all devices that carry this data and facilities where these devices are located.
This part includes the following standards:
- Facility Access Controls;
- Workstation Use;
- Workstation Security; and
- Device and Media Controls.
Let’s go over each of them.
Facility Access Controls
This standard is basically about procedures to give authorized people access to facilities and equipment and to ban access for unauthorized individuals.
This involves:
- Contingency operations, an emergency or disaster recovery mode where authorized individuals should be allowed to the facility to recover the data;
- A Facility Security Plan outlining measures you will take to protect the facilities and equipment (like door locks, surveillance, alarms, property tags, personnel and patient badges, etc.);
- Access control and validation procedures to allow or ban access to facilities and software based on a person’s role (personnel and visitor control);
- Keep maintenance records of all security-related repairs of the facilities and equipment.
Workstation Use and Security
These HIPAA standards imply that you have to outline clear rules for the use of workstations. Any device that an employee can access protected patients' information from (PCs, laptops, mobile phones, and tablets) can be considered a workstation. Also, you need to make sure that these rules apply onsite as well as offsite for instances when employees work from home.
This includes:
- What equipment can be used as a workstation;
- Where it can be placed/used;
- Who can access what equipment;
- What privacy measures should be used, e.g. automatic logoffs, password-protected screensavers.
Device and Media Controls
This standard concerns all data storage devices that you and your employees use to store ePHI. These can be hard drives, memory cards, and memory sticks that you can use with your workstations.
Here is what you have to clear out:
- How are you going to dispose of the memory devices that are no longer needed?
- How do you properly remove ePHI so that the devices can be re-used?
- Does it make sense for you to track movements of all devices and media and the people responsible for them?
- In what situation should you or your employees create a backup of ePHI before moving the equipment?
5. Technical safeguards

Technical safeguards are requirements and policies for the technologies you use in your practice to store and transmit ePHI.
The rule doesn’t oblige you to use any specific apps, but rather sets general guidelines and it is your job to determine how to apply them in your practice.
It consists of the following standards:
- Access Control;
- Audit Controls;
- Integrity;
- Person or Entity Authentication; and
- Transmission Security.
Access Control
The technical part of Access Control covers how the rules we discussed above (about who gets access to what information) should be implemented in your software.
There are four specifications as to how you should control access to ePHI:
- Have unique user identification, like a unique user name or number or both;
- Determine who should access ePHI in case of emergency and how he/she should do it;
- Have automatic logoffs when a user leaves or gets distracted for some time;
- Encrypt parts or all of the information.
Audit Controls
HIPAA also obliges you to log everything that happens in your information systems and review these logs regularly. The rule doesn’t specify which information and activities should be monitored but leaves it up to you to decide on the most critical things to audit (in accordance with your risk analysis).
You can automate all or part of your audit with special apps or do it manually. Therefore, you need to decide:
- What information and system activities do you need to audit?
- What audit mechanisms are reasonable for your practice?
- Does your EMR have audit functionality? If so, is it sufficient to comply?
Integrity
You know how dangerous it is when a patient's health data is inaccurate due to someone’s mistake or fraud. This can lead to all sorts of bad consequences for the patient, including his/her safety. That is why this standard requires you to protect the integrity of patient information, preventing it from being improperly changed or deleted.
To protect the integrity of ePHI, you need to:
- Have a way to authenticate electronic health information to automatically check whether the data has been changed or not.
Person or Entity Authentication
To effectively control access you also need to be able to automatically verify that the person is who she says she is. For this, you need user authentication.
You can authenticate users in the following ways:
- Require something only known to the user, like a password or PIN code;
- Require something that only the user has, like a card or key;
- Require biometrics, like fingerprints or facial patterns.
Transmission Security
Finally, you need to ensure your patients’ information is safe while it is transmitted via the internet or some private networks.
Under this standard you need to ensure that:
- The information doesn’t get changed or lost while it is transmitted (Integrity);
- Information is encrypted when needed (when the risks are high).
Are you satisfied with the way you keep your electronic medical records? Let’s talk about building a custom EMR that is secure and satisfies 100% of your needs!
Contact Us6. Data Breach Notification

If you experience an uncontrolled leak of patient information, you will have to report the breach of protected health information.
Data breaches are not limited to technical errors or data thefts, but also include:
- emails sent to the wrong or open list of recipients;
- unlawful publication of patient data;
- loss of physical records; and
- access to protected information by an employee without necessary credentials.
Depending on the circumstances, you will have to inform:
- Affected patients - notify the patients within 60 days after the discovery of the breach that their records were compromised, explain the details of the breach and measures to mitigate further consequences;
- The U.S. Department of Health and Human Services (HHS) - submit the same notification to the regulatory body on an annual basis; and
- If a breach affects more than 500 individuals from one State or jurisdiction, inform local media outlets and submit the information for publication on the HHS Website within 60 days.
How to Apply This To Your Practice
By now you’ve probably guessed how much liability you get together with patient information.
Like it or not, you will need to put a lot of thought and resources into protecting your patients’ data and comply with HIPAA. The key things to consider are:
- What information you really need;
- How you are going to collect and use the data;
- What information you can and cannot disclose to various parties;
- Prepare and implement procedures and policies to protect PHI administratively, physically and technically;
- If a breach does occur, how you will notify all the necessary parties as soon as possible.
If you think this is too much for you to handle on your own, call us for help.
How We Can Help
We can help you with:
- Preparing your practice for HIPAA compliance;
- Building a HIPAA-compliant EMR from scratch.
The team at Greenice has experience in building EMRs for various types of medical practices, including psychotherapy. We can help you build an EMR that is tailored exactly to your needs and your unique process of serving patients, and we will make it secure and HIPAA compliant.
We’ve also teamed up with Legal Nodes, a legal advisory company, to provide an all-around HIPAA-compliant solution for your mental health practice. Their network of tech-savvy lawyers has substantial experience in ensuring legal compliance of IT businesses and solutions in more than 20 jurisdictions, including the US, the EU, and Asia. Legal Nodes can help you with preparing necessary policies, privacy notices, and agreements for a HIPAA-compliant Mental Health Practice, as well as with navigating the road to compliance.
 Co-Author: Vlad Nekrutenko is a Privacy Lawyer at Legal Nodes. He gained experience in consulting tech companies on personal data protection and, more generally, e-privacy compliance in a variety of countries, including the European Union, the United States, and the Eastern Europe countries.
Co-Author: Vlad Nekrutenko is a Privacy Lawyer at Legal Nodes. He gained experience in consulting tech companies on personal data protection and, more generally, e-privacy compliance in a variety of countries, including the European Union, the United States, and the Eastern Europe countries.
Get a Free Consultation on HIPAA compliance for your Mental Health Practice
Contact UsRate this article!
Not rated







 Sign in with Google
Sign in with Google
Comments (0)